When you think about your social media accounts – let’s say your Facebook password – does it have anything in common with your LinkedIn or bank account password? Does it have the same password as your corporate account? If so, you are not alone! According to a Google survey, at least 65% of participants re-use their passwords across multiple accounts and web services.
As every service, website, and social media account requires a password, many people find it easier to reuse the existing ones instead of reinventing new ones, especially since it is difficult to manage and memorize multiple passwords. This is particularly true as, due to security policies, passwords are, by necessity, becoming more and more complex. Although most of the population understands the risk and knows that one shouldn’t reuse passwords, most of us continue reusing passwords for both corporate and personal accounts.
Some people use password managers, which are considered safe, to help them store their credentials. However, these tools are not bulletproof, as seen in August 2022 when LastPass was breached for a second time. On that note, in a survey from 2022, another password manager service, Bitwarden, found that 84% of the service consumers use the same password across multiple business and personal platforms.
India according to Statistica, there were around 170 cases of data theft reported across India in 2021, a huge jump when compared to the 98 reported in the previous year. Such a huge jump could possibly be attributed to the accelerating digital adoption over the pandemic, which forced many organizations online. With this drive to go digital, organizations and individuals also lack cybersecurity awareness leading to increased cybercrime.
It’s not surprising that cybercriminals immediately saw an opportunity presented by people’s generally lax behavior regarding password reuse and created a flourishing underground market of databases obtained from breached websites.
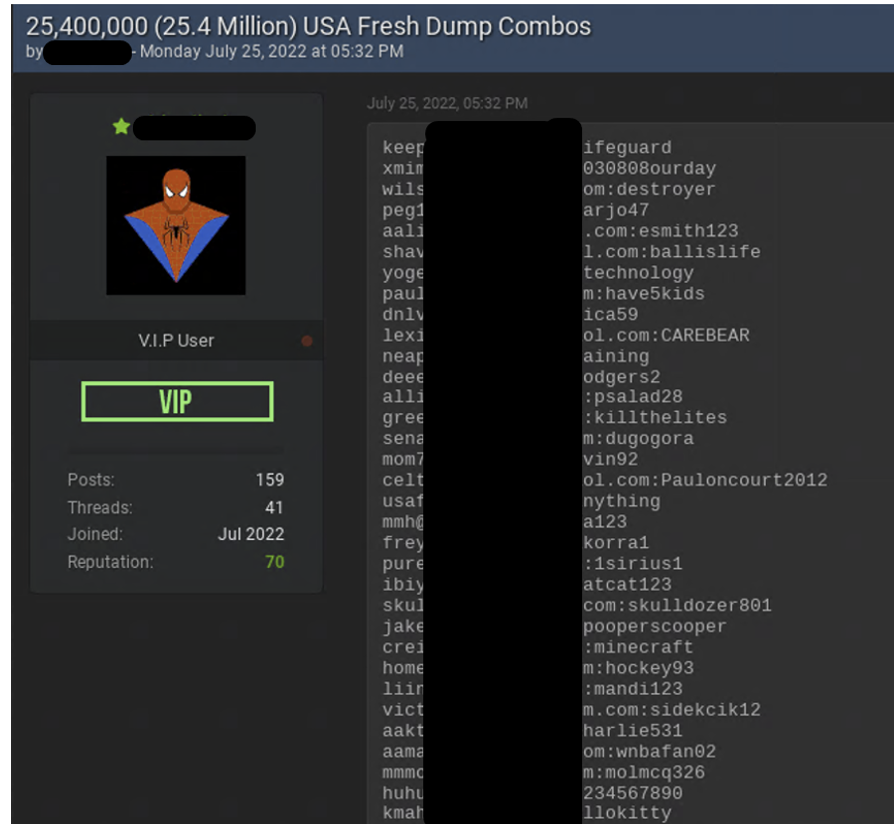
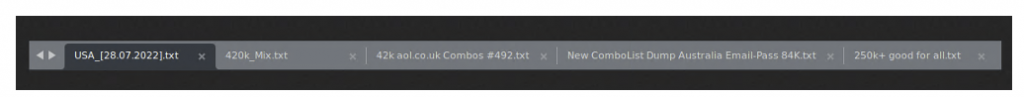
As most cybercriminals do not care about the origins of the credential pair, they create “combo lists”, huge compilations of many stolen databases that are just lists of email addresses and passwords. Many of those are lists of corporate email accounts with passwords that were used on 3rd party services. The largest combo list of all time, called RockYou2021, was published in 2021 and contained more than 8 billion unique sets of email accounts and passwords.
Credential Stuffing Attacks – How do threat actors leverage stolen credentials and combo lists?
Credential stuffing is a type of cyberattack in which the attackers collect stolen account credentials, typically consisting of lists of usernames and/or email accounts and the corresponding passwords. They then use the credentials to gain unauthorized access to user accounts through large-scale automated login requests directed against a Web application.
Credential stuffing is one of the most common techniques to take over user accounts, including emails, banking accounts, social media, and corporate accounts.
The Underground Perspective
As soon as cybercriminals understood the big business potential of stolen passwords, they started focusing their efforts on hacking different websites and services that are not of great value by themselves – but are lucrative because of the user credentials they contain.
The NIST password storage guidelines require that passwords be salted with at least 32 bits of data and hashed with a one-way key derivation function. However, even in 2022, many websites don’t comply with this policy and some even store passwords as plain text records.
The cybercriminals who hack these websites are not necessarily the ones who most effectively use them. Many flourishing underground communities and markets were created around buying and selling stolen data and credentials. Valuable sets of credentials that provide administrator-level access to an organization can cost up to $120K in the underground, with an average of $3K for administrator sets. While many sets of credentials are sold in the underground forums, many are also given for free.
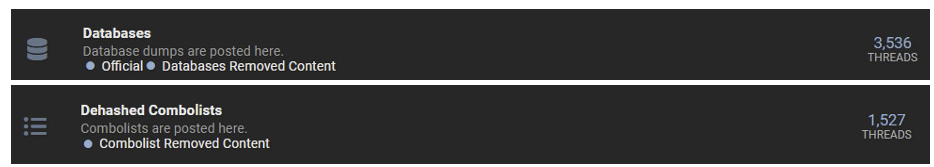
In just the last six months, in one of the prominent English-speaking underground communities, more than 3,500 threads concerning stolen databases were opened, and more than 1,500 threads about combo lists that include just email accounts and passwords. Each one of these databases can include millions or even hundreds of millions of credential sets.
While those databases and combo lists include a high percentage of webmail credential sets whose exposure poses only a low risk to the corporation, they also include many sets of corporate email accounts with passwords that employees use to register on 3rd party websites. This is the Holy Grail for the cybercriminals, the most valuable quarry of them all. When the same password is used across personal and business accounts, the damage potential of a cyberattack increases as criminals can access multiple accounts when just one is breached, and the organizations’ vulnerability to cyberattacks increases. These accounts and applications lie beyond the visibility and protection of business IT teams.
In many cases, cybercriminals also separate the combo lists according to the country to make it much more convenient to use.
How does Check Point Harmony Browse help you prevent the re-use of corporate passwords?
As a complete web browsing solution, Harmony Browse offers credential theft prevention by blocking the re-use of corporate passwords across multiple web services. Password reuse is only one example of how the workforce often unwittingly puts their organizations at risk. Harmony Browse offers extensive web browsing protection to ensure your organization is protected from Web-borne security threats. Among its features, the solution prevents users from visiting phishing sites or downloading malware without compromising workers’ productivity. Organizations need to start taking that first step toward a more data and credentials-secure world.
(The author is Harish Kumar, Head of Enterprise at Check Point Software Technologies and the views expressed in this article are his own)
Also Read: Metaverse Reality Check: Is It Worth It?