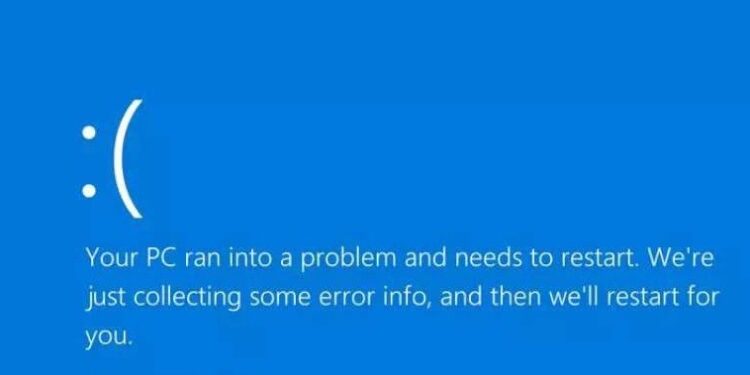
The Blue Screen of Death (BSOD), also known as a stop error, is a critical error screen that appears on Microsoft Windows computer systems when the system encounters a serious issue that it cannot recover automatically. This error indicates that the operating system can no longer function properly to prevent further damage. Your computer might display a message such as “Windows has been shut down to prevent damage to your computer”
Third-party updates and malicious software that can interrupt system processes or corrupt essential files can cause a Blue Screen of Death error. These updates can introduce new bugs, application conflicts, or compatibility issues that disrupt system stability. System hardware and software issues can also lead to these errors.
“When your Windows computer displays a Blue Screen of Death error, it’s usually because something went wrong and required your attention immediately for further use. Sometimes, it only shows an error message, but sometimes, it shows an error with the code and details description, which may help understand the issue and help fix it.
Blue Screen of Death impact on your computer
The Blue Screen of Death forces the computer to stop all operations, preventing further activity immediately.
Repeated system crashes can strain hardware parts due to this error. Excessive heat, a common reason, may harm some crucial components such as the motherboard, RAM, or hard drive.
Due to Blue Screen of Death, critical read/write operations can corrupt system files and application data. Such a situation can cause instability in both applications and system behavior.
When a Blue Screen of Death occurs, any unsaved work or data in your computer, laptop, or applications is lost. If malware causes a Blue Screen of Death, it signals a security weakness that requires attention. An unstable system is at a higher risk of security breaches. You can mitigate these risks by taking proactive measures such as creating restore points, backing up data, and testing updates.
Follow the Microsoft guidelines to resolve the Blue Screen of Death error issue.
Also Read: Do Our Abilities Match the Ambitions of Smart Cities?