Malware is a harmful intentionally created software, developed to cause harm, data steal, spying, hacking, application interruption to a computer, network, server etc. There are different types of malware. How to remove malware is not as easy as normal virus infection Because An advanced malware might simply hide deep in your system using advanced rootkit techniques meaning the same might go unnoticed by your antivirus software. You can safe yourself from malicious attack in today’s online world by following below steps.
Symptoms of Malware Infection
Before Stepping on how to remove malware, lets make sure it is malware or other normal virus infection or just nothing.
1. Slow System Processing – Malware is designed to use up as much as the processing power of a computer as it possibly can. In case your system is performing poorly irrespective of having a good configuration, it might be infected with a malware.
2. Unusual Behavior. If system is infected with malware, certainly it will behave randomly unusual. It can give fresh new command and close you current application. It may result from a malfunctioning program that runs at computer machine startup.
3. Frequent System Crash – Malware causes conflicts with the general processes of other critical programs in your computer which causes system instability leading to Blue Screen of Death. By following below mentioned steps on how to remove malware will help you out from BSOD. When a PC crashes on a regular manner, chances are high that it might be the result of fatal hardware failure or malware infection.
4. Suspicious Unknown Activity. If you open log file directory it may show you many unknown activities which you never instated. Some malware can run and actively harming computer in background process.
5. Popups. Once you connected with internet, it may add lots of new items in tool bar. And continuously show you irritating random popups and harmful advertisement. Follow how to remove Malware steps will sure help you to get rid of these annoying popups.
6. Automatic Execution and Termination of Programs. In case your system is opening and terminating processes, programs, etc. on its own, may be malware infection is behind it all.
How to Remove Malware, Step-by-Step Guide
Now, if you are sure it is malware any specious activity but not sure weather it is malware or any else harmful virus. Get rid of it completely is the only solution to keep you safe, Because if it is there it can steal anything from your computer and believe me you would not know that. Few viruses are so dangerous, not a easy task to detect and remove.
1. Physically Disconnect Your System From Internet
If you are in suspicion or sure that your system is a victim of a malware attack, the first order of business is to physically unplug the same from any connected network. It can either be your Wi-Fi router, or your broadband connection.
Sooner you disconnect your device from the internet is the better as it helps to put an end to your sensitive data from being transmitted to the cybercriminal via the internet. Unplugging is one of the best ways to put an immediate end to an ongoing cyber attack!
2. Boot your PC into Safe Mode
Safe mode is a diagnostic mode, Here only the critical programs and processes are loaded which makes it harder for a malware to load itself and execute as soon as windows starts. As the harmful files are not active, it becomes easier for you to remove them from your system.
To Enter safe mode just restart your machine and press f8 key, keep pressing until window loads with safe mode. Or you can use Networking method to enable safe mode.
3. Check Installed Programs
This window has a complete list of all installed software in you computer machine. Go to the installed program tab ( Control Panel -> Programs -> Programs and Features ). Just look complete list of installed items to make sure there are none suspicious or unknown software installed in your system. If you found any try to uninstall it.
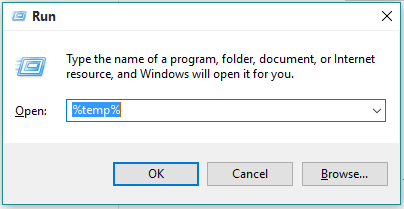
4. Clear temporary files from your system
you can either use your computer’s inbuilt disk cleanup utility. Or you can manually do the same by pressing window+r key and after typing %temp% press enter key in your run window which will open your system’s TEMP file folder. Clear all the content present in the folder which will also remove any residual files of malicious nature.
5. Police Your Online Behavior
One should be vigilant while surfing the internet and be wary of what exactly they are clicking on. Just clear the cookies from your browser. It is best to avoid websites that might be suspicious to look at or might be blocked by your antivirus software. If your AV is blocking access to any particular website, it is best to avoid the same altogether! Be sure to keep the OS of your device updated so that vulnerable points in the same are patched shut!
6. Scan Your Device Using a Reputed Antivirus
Completely scan you system with reputed antivirus. It might take few times but there is no other way. What many users often fail to understand is the importance of using reputed antivirus software and to keep the same updated. Antispyware and antivirus software is your first line of defense against a malware attack or other cyber attack. It is advised to run periodic scans of your system so that your device is free from any malware that might have got unnoticed for some time now.
If the Antivirus detected malware then simply remove it and scan again if it is showing your are safe signal then you are safe, you removed it easily.
7. Run Malware Detector Tool
With the temporary folder empty the malware is unable to execute its nefarious processes designed to harm your system and steal sensitive data. Now there is higher chance that malware detector tool or Malwarebytes will surely detect and help you to get rid of it. You can free download Malwarebytes (malware detecting software)
What if Above Mentioned Steps Could not Solved Issue:
It should be kept in mind that scanning and cleaning your system using an antivirus works only for standard infections. In case your system is severely attacked by a harmful malware of unknown origin, and the above steps how to remove malware would not work. The last resort is to go for a full system format. It is best to format you system and reinstall the OS. It is one of the best options to rid your system of advanced malware.
Conclusion
By following how to remove malware , you could remove malware infection but one should be vigilant while surfing the internet and be wary of what exactly they are clicking on. It is best to avoid websites that might be suspicious to look at or might be blocked by your antivirus software. If your AV is blocking access to any particular website, it is best to avoid the same altogether. Be sure to keep the OS of your device updated so that vulnerable points in the same are patched shut. All in all, if one follows closely the above-mentioned pointers they can help their device to bounce back from a malware attack in minimal time delay.



















