Microsoft Azure, the foremost leader in the cloud computing service provider, has been affected by significant security flaws. Check Point researcher identifies two major security flaws on January 30, 2020. Researchers team recognizes that a Microsft Azure network user could have possibly taken control of the complete server, and unlocking a path to business code theft and manipulation.
Nothing to worry, Check Point and Microsoft teams worked together and fixed both the security flaws.
The first security flaw was discovered in Azure Stack; this would have enabled a cybercriminal to capture screenshots and can steal relevant confidential data from the device operating Microsoft Azure.
The second security flaw was found in the Microsoft Azure App service, this flaw would have enabled a cybercriminal to take control of the whole Azure server and consequently gain access over the enterprises’ business code.
How Check Point Identifies Microsoft Azure security flaws
First, Check Point researchers install Microsoft Azure Stack Development Kit (ASDK) on their server, then they mapped the places they thought they might find vulnerabilities around. Since Azure Stack has similar features to Microsoft Azure’s public cloud, researchers focused on those vectors.
Disclosure
After the identification process, researchers shared its finding with the Microsoft team. Check Point team disclosed the first security flaw on January 19, 2019, in which Microsoft created CVE-2019-1234. The second security flaw was uncovered by Check Point on June 27, 2019, in which Microsoft created CVE-2019-1372. They bothe, Check Point, and Microsoft worked hard to fix these flaws. Full patches for both security flaws in Azure were issued to the public by the end of 2019.
- Also Read: Enterprise Cybersecurity Threats in 2020
Microsoft Azure Security Flaws
1. Azure Stack security Flaw
Azure Stack, a cloud computing software solution built by Microsoft to empower enterprises to deliver Azure services from their personal owned data center. Microsoft created the Azure Stack as a way to encourage businesses to adopt hybrid cloud computing by providing the power of the cloud while still being able to discuss business and technical effects like regulations, data sovereignty, customization, and latency.
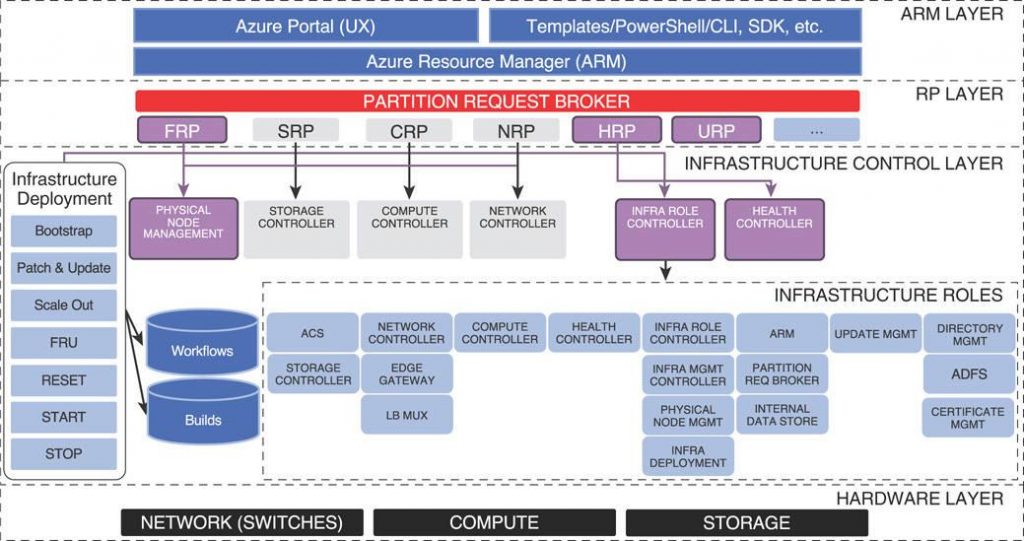
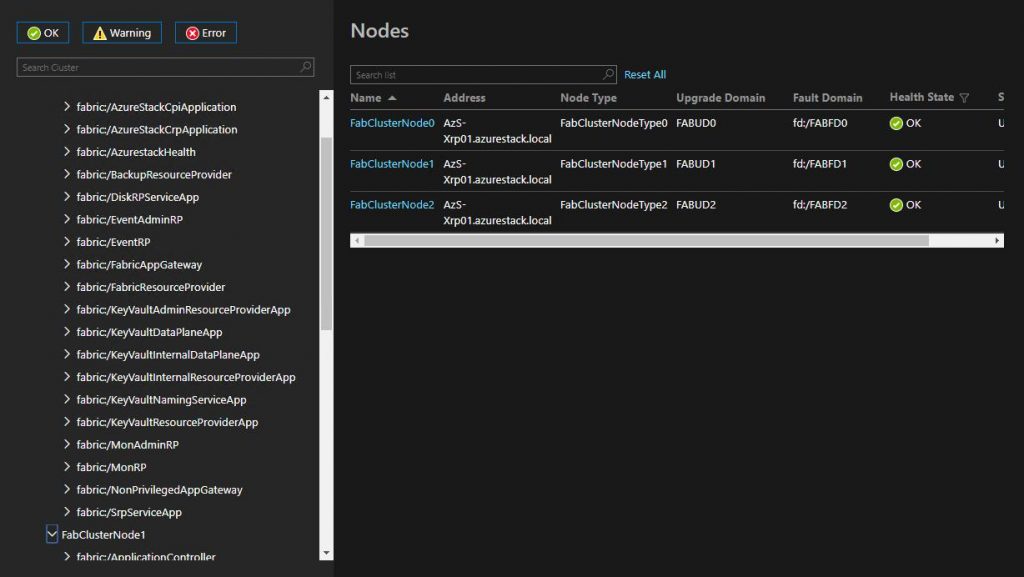
Check Point teams got passage to take screenshots and disclose relevant information of Azure tenants and infrastructure devices. This security flaw would allow cybercriminals to get information on any business that has its device running on Azure software. To perform the exploitation, a hacker would first obtain entrance to the Azure Stack Portal, enabling that person to send unauthenticated HTTP requests that provide screenshots and data about tenants and infrastructure devices.
Screenshot capturing and information disclosure
2. Microsoft Azure App Flaw where Attacker Gets Control of entire Server
Microsoft Azure App Service is a wholly managed “Platform as a Service” (PaaS) that combines Microsoft Azure Websites, Mobile Services, and other services into a single service, adding new capacities that enable integration with on-premises or cloud systems. Microsoft Azure provides users capabilities like as provisioning and deploying web and mobile apps, build engaging iOS, Android, and Windows apps, automating business processes with visual design experience, and integrating with “Software as a Service” (SaaS) applications like Salesforce, Marketo and DropBox.
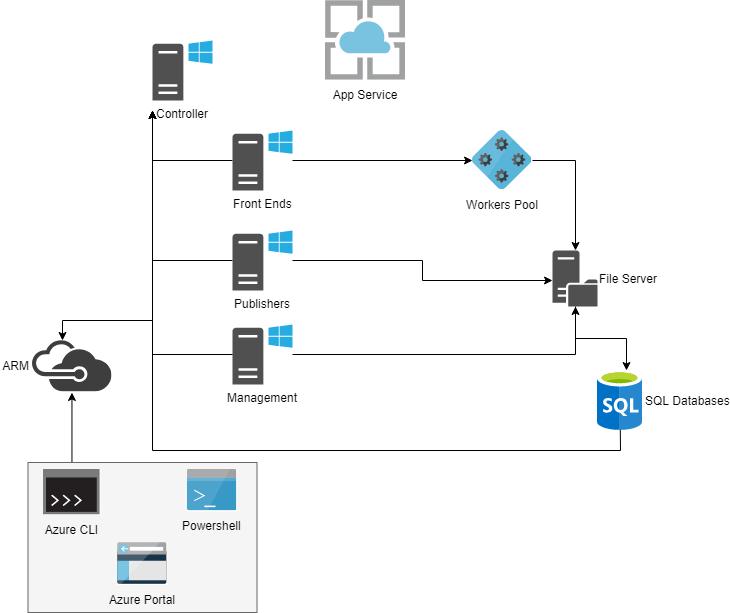
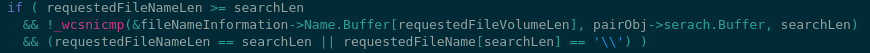
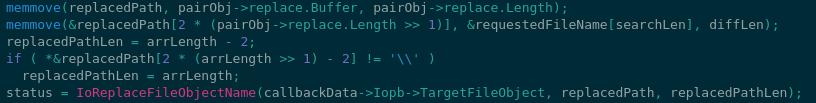
Azure App users might be aware they can explore home directory by command D:\home, have you tried how it works?, how all tenant app approach own home directory by locating this path? The answer lies in the PreFilterOnCreateCallback function. We discussed before on the SandboxSettings structure, one of its properties is called sandboxRemotePath which contains a UNC file share path to the storage location of the app. DWASSVC sets this path at the start of the IIS worker process by interacting with the driver using the disclosed filter port (FltPort). So when the app tries to access D:\home or other special paths, the filter driver matches and replaces them with the exact ones on the fly.
Check Point researchers were able to determine that a cybercriminal could settle tenant applications, data, and accounts by creating a free user in Azure Cloud and running malicious Azure functions. The end result would be that a hacker could potentially take control of the whole Azure server, and consequently take control over all your business code.
- Also Read: Cost of Data Breach at the End of 2019