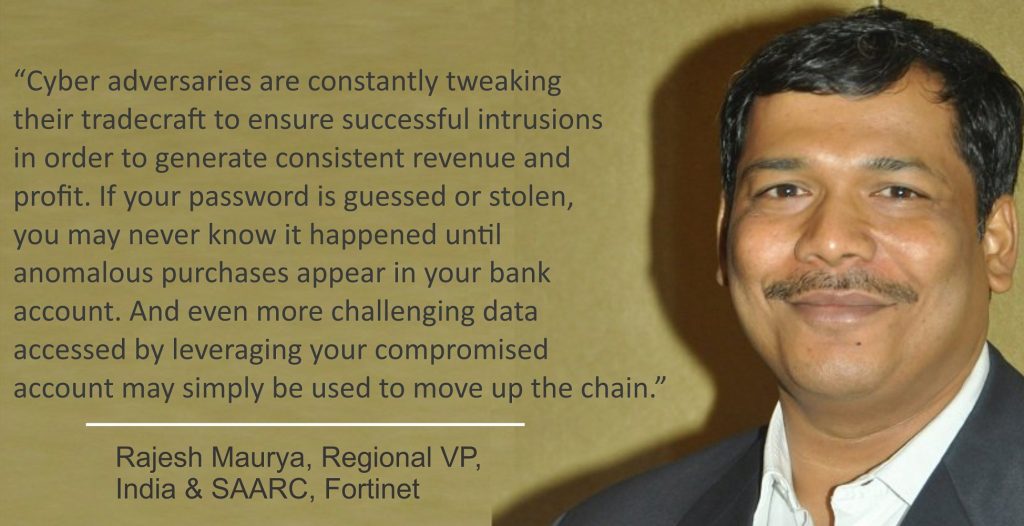
In this digital era, you might have to protect many devices and accounts, In many cases one just go with random common password. You should not give a chance to cyber criminals to enter into your accounts, week and random used passwords are the main cause of many data breaches and hacks in 2018. Cyber security company Fortinet issued password security guidelines for its team members and stakeholders to go with a password strategy to protect corporate data.
According to the Verizon Data Breach Investigations Report, 81% of breaches leveraged either stolen and/or weak passwords. That problem is compounded because one of the biggest risks to data security is the reuse of passwords across accounts. If one of the accounts is compromised and your user name and password are posted on the dark web, cybercriminals who know how often passwords are reused will simply begin to plug that information into other possible accounts until they unlock one that uses the exact same credentials.
Hackers are advancing with advancement of technology. Easy Short password carries big risk with it, and for the hackers it won’t take much effort and technology to crack it. In fact, hackers maintain databases of the most common used words, phrases, and number combinations that they can run your password through to find a quick match.
To protect your password security you need to make it strong, and must avoid direct names, sequencing numbers, date of birth etc. To make your data and accounts secure, you need to follow below password security guidelines.
6 Best Password Security Guidelines
1. Adding extra layer of security and multi factor authentication always preferable, go with it wherever it is applicable. This confirms your identity by utilizing a combination of multiple different factors, such as something you know or something they have, such as a token generator on your smartphone.
2. Each account must have different password, do not repeat one password for multiple accounts.
3. At least in every three months you should Change your passphrase. This will lock out cybercriminals who may be using your account, protect you from brute force attacks, and remedy the issue caused by cybercriminals who purchase lists of usernames and passwords obtained through data breaches.
4. Maintain the privacy when you enter the password, ensure no one is watching.
5. Be cautious when downloading files from the internet as they may contain key loggers as well as password grabber malware variants that will compromise your password. A good practice is to regularly scan for the presence of such malware.
6. Use a cloud-based password manager to enable you to create and store strong passphrases. This is especially important if you require strong passwords for dozens of accounts. Password management tools allow you to securely store an encrypted list of passwords in the cloud that can be accessed from any device. Not only will you only need to remember one password to access your password locker, the passwords you store there for your various accounts can be even stronger because you don’t have to remember them.
10 most common online passwords
- Password1
- Welcome1
- P@ssword
- Summer1
- password
- Fa$hion1
- Hello123
- Welcome123
- 123456
- 123456q@