COVID-19 continues to make a harmful impact on our economy and life worldwide. As per Dr. Anthony Fauci, – longtime director for the National Institute of Allergy and Infectious Diseases and the emerging face of American leadership in the fight against the virus – it is estimated that the U.S. may see between 100,000 and 200,000 deaths from the coronavirus.
And in cybersecurity in COVID-19, security-related incidents and attacks are continuously increasing. As earlier reported, while retailers and other non-essential firms are closing their doors, cybercriminals are opening up for business, with the number of COVID-19 related cyberattacks on the rise.
Based on ThreatCloud, Check Point’s industry-leading threat intelligence engine, our researchers found that though cyber-attacks, in general, have decreased somewhat since the outbreak and economic downturn, COVID-19 related attacks have increased significantly.
From January to March, we witnessed a drop of 17% monthly in the overall number of cyber threat activities in organizational networks worldwide.
However, since mid-February, we have seen an escalation in the number of COVID-19 related cyber-attacks, and in the past 2 weeks alone, the numbers have increased dramatically from a few hundred daily to as high as over 5,000 on March 28. On average, there have been over 2,600 attacks daily.
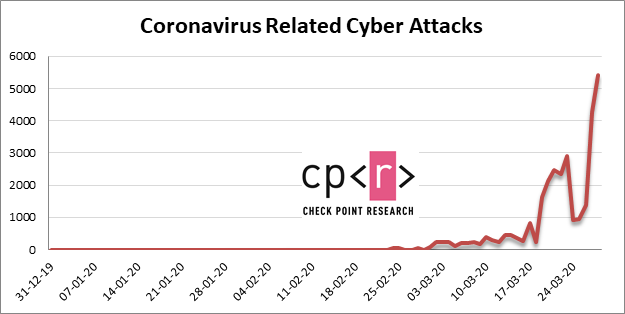
The graph represents all COVID-19 related attacks that have been detected by Check Point’s different Threat Prevention technologies across networks, endpoints and mobile devices.
84% of the events were triggered by phishing websites. Approximately 2% of the events involved the victim accessing the malicious website using his/her mobile device.
In the past two weeks, since our last update, more than 30,103 new COVID-19 related domains were registered, of which 0.4% (131) were malicious and 9% (2,777) were suspicious and under investigation. This means over 51,000 COVID-19 related domains in total have been registered since January 2020.
Netflix-related websites
While it is not surprising that the pandemic has resulted in Netflix’s subscriber growth, the brand has been used as part of various web-based fraud schemes. In recent weeks in particular, we have observed a substantial 2x growth in the number of phishing attacks by websites posing as Netflix sites. Most of these sites were registered in recent months, including domains that use the virus’s official name given by the World Health Organization (netflixcovid19s.com).
Some of these websites offer payment options, in attempt to fraudulently get user details and their payment means.
Here’s an example:
Staying protected
So how can you avoid falling victim to these scam attempts? Our recommendations for safe online behavior are:
- Beware of lookalike domains, spelling errors in emails or websites, and unfamiliar email senders.
- Be cautious with files received via email from unknown senders, especially if they prompt for a certain action you would not usually do.
- Ensure you are ordering goods from an authentic source. One way to do this is NOT to click on promotional links in emails, and instead, Google your desired retailer and click the link from the Google results page.
- Beware of “special” offers. “An exclusive cure for Coronavirus for $150” is usually not a reliable or trustworthy purchase opportunity. At this point in time, there is no cure for the coronavirus and even if there was, it definitely would not be offered to you via an email.
- Make sure you do not reuse passwords between different applications and accounts.
- Organizations should prevent zero-day attacks with an end to end cyber architecture, to block deceptive phishing sites and provide alerts on password reuse in real-time.
Source: Check Point Research
Also Read: Data Protection and Compliance While Working From Home